This is complete step-by-step configuration instructions for setting up VPN connectivity (L2TP/IPSEC) between Zywall USG firewall and the client devices including Windows Phone, iPhone/iPad and Android or Win 10 OS.
For those not fully aware about the advantages VPN will give you – it will enable an encrypted pipeline to your home/office network, and you can use all the services/devices in your private network in safe and secure manner, without opening unnecessary ports that would increase the level of vulnerability of your private network.
Examples of VPN usage:
- Connect and use internet and online services in encrypted and secure manner from not-trusted environments like cafes and public WiFis.
- Stream freely from anywhere your private videos, view your private photos or work with any computer/document that is available in your network.
- View and access country-level regulated online materials from your VPN ‘home’ location when traveling abroad.
- Connect to you surveillance cameras, wildlife trail cameras or home alarm systems.
Find below step-by-step configuration instructions for enabling above:
Zywall:
1) Setup and ensure/add that ports required by VPN connectivity are defined and available (NO other SERVICES that are utilizing the same ports!):

2) Create VPN User (Object/User tab) and VPN Group (ObjectGroup tab), and add created user into the Group:

3) Create WAN, L2TP_POOL and LAN addresses accordingly (L2TP range TO BE completely outside any home/external IP range, that might be in use in either end of the VPN tunnel during VPN utilization – otherwise you may expect trouble…):


4) Create IPSEC VPN gateway (create own or utilize default available, link then to VPN connection created below):

4) Detailed configuration example:
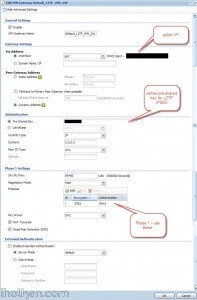
5) Create VPN connection that uses above created VPN gateway (you can utilize default available or create own):

5) Detailed configuration example:

7) Create required firewall rules. Make sure VPN required services/ports are allowed (for example IKE, default rule in Zywall). Allow from IPSEC/VPN to LAN or to ANY, depending if wanted through VPN access only to LAN or also to internet:

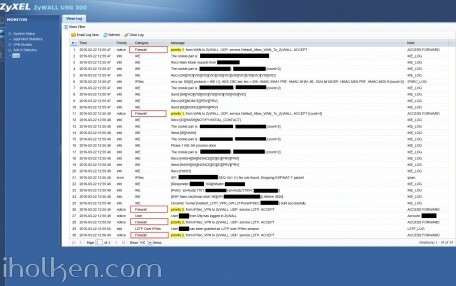
Firewall rules has critical role in establishing the tunnel and allowing the traffic through the tunnel. Please find below for VPN connection ‘negotiation handshake’ troubleshooting purposes an example of successful L2TP/IPSEC handshake flow extracted from Zywall log, and the parts where firewall rules play critical role:
If you have any issues with your firewall, please enable logging for correct steps and investigate the zywall logs – they are extremely useful.
8) Create required routing rules. (IF ‘send all traffic’ through VPN is on (meaning internet through VPN) – you also need to setup the Policy Route that is upper in the table below:

9) Keep WAN trunk and SNAT enabled:

Client Machine:
10) Configure client machine – below example Windows Phone 8.1+:


Test Connectivity:
11) Test and confirm VPN by accessing your private network through 4G VPN connection (lock indicator). Also internet addresses are available through VPN, if allowed in firewall and routing table.


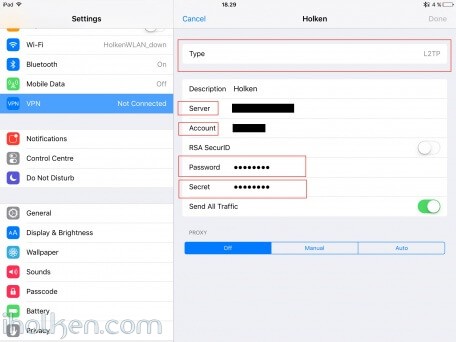
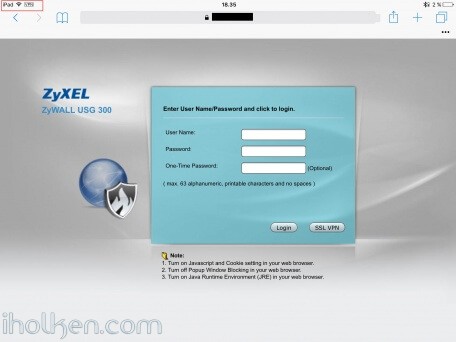
12) Configure client machine – below example for IOS (IPhone or IPad):
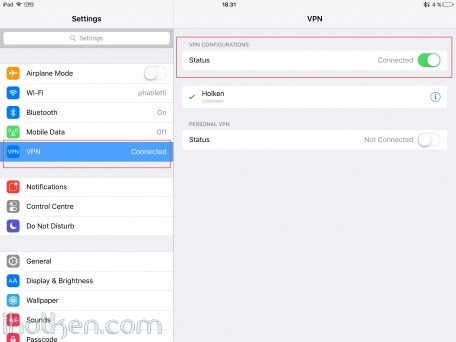
Test Connectivity:
13) Test and confirm VPN by accessing your private network through VPN connection (lock indicator). Also internet addresses are available through VPN, if allowed in firewall and routing table.
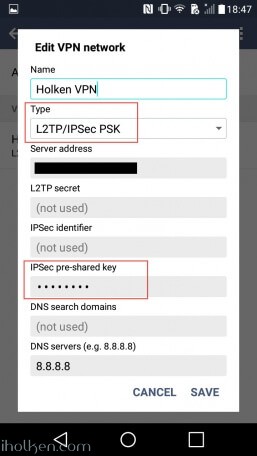
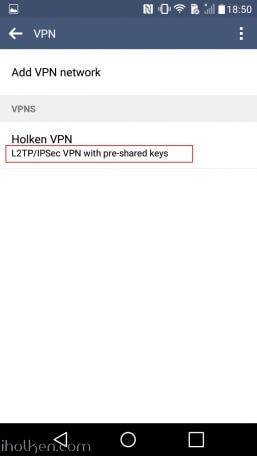
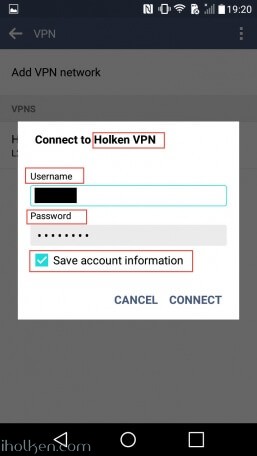
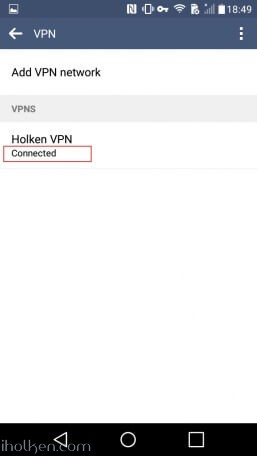
14) Configure client machine – below example for Android (Lollipop sw):
Test Connectivity:
15) Test and confirm VPN by accessing your private network through VPN connection (lock indicator). Also internet addresses are available through VPN, if allowed in firewall and routing table.
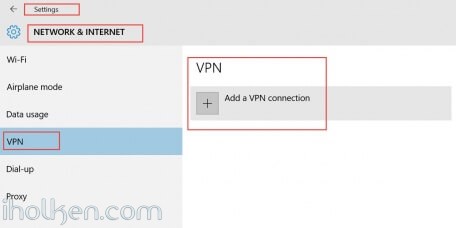
16) Configure client machine – below example for Windows 10 Operating System:
Navigate to: Start –> Settings –> Network & Internet –> VPN –> Add a VPN connection
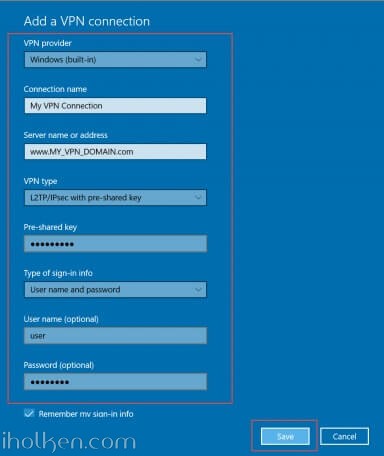
Then give the required connection details for the connection and hit Save:
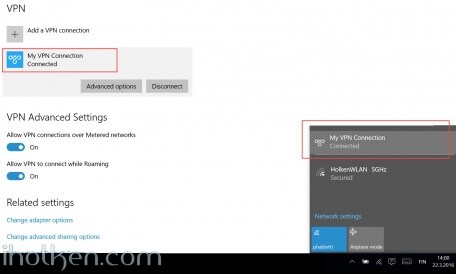
Now you are able to Connect to the VPN tunnel – through Network Settings or System Tray, and see ‘Connected’ indicator:
And that’s it!
Now you have configured the Zyxel Firewall for VPN connection with L2TP/IPSEC and client device being WP or IOS / Android Device or Win10 OS.
If this helped you in getting your VPN connection built, please drop me a post below for confirmation – Thanks!!! 🙂






Question ,
i have 3 USG 1000 firewalls first one has firmware 3.00 and the other has 3.30
i setup the first firewall , this one is online and running, the VPN is working fine !
the other 2 , i restored the settings from the first firewall, ( these other 2 are offline )
if i want to connect the default VPN, it gives an error ( 16015 dial a dynamic tunnel has failed crypto )
is this because it,s not connected to the internet, or is this firmware related ?
thanks
how to setup the client for using the vpn, but using the internet only local ( so not the zywall connection )
is this firewall related or routing
Hello Juha,
have you tried with users from Active Directory?
I am failing with AD users. Local users are working perfectly.
Best regards
Christian
HI there!
It works! But when you are connected to a VPN there is no available internet access on the connected device.
Cheers,
Andy.
Yes, like Andy said. I¡m trying to resolve but nothing is shown in logs.
Well, simply put the firewall rules in the order the screenshot shows. Rules are evaluated in order so I had a lot of them before and didnt work. Now it’s working flawessly from iPhone and PC.
Thank you all.
Hi, Juha.
Amazing guide – so helpful! Thank you!
I’m struggling with one problem that I wonder if you could point me in the right direction:
I can connect two remote PCs to the VPN network with ZyXel USG40. Using (remote) Windows 10 PCs, I can browse files on either of the two PCs over the VPN by typing the IP/share into the address bar, but I can’t see any of the files on any PCs on the local lan at the location where the USG40 is, nor can the local lan PCs see files on the remote PCs. Remote PCs are correctly assigned VPN subnet IPs, while the local lan has PCs on its own subnet. I can’t seem to create a working policy route that will allow me to cross the LAN1-VPN divide!
Any suggestions you might offer would be greatly appreciated.
Cheers.
Len
Hi Juha!
Just want to drop you a line and say BIG thank you! Works great on usg 50 – I’ve been trying all the YouTube and Zyxel how tos and it hasn’t worked which was very frustrating- your guide is spot on and works from the first try! 🙂 Cheers and God bless you and the internet. It’s inspiring to share for the greater good!
Awesome write-up. I found a small problem. If you have an existing multi-site VPN, it could stop working if you create firewall rules as described because they limit the traffic between the sites. I already had a rule that covered site-to-site VPN, same rule worked for the new client tunnel.
One thing that I could not get to work is multi site. The client had access to the site it VPN’d to, but can’t ping anything from other sites. If you could cover this part of setup, I and I am sure others will be eternally grateful!
Very nice… thanks for putting this all together. It helped explain a lot after reading several articles and sites scattered around the net. To be sure, I followed similar steps from the zyxel PDF below and had trouble before I found your guide. After stepping through your suggestions found that I forgot to enable the VPN gateway and/or connection for the zyxel process. =)
http://www.zyxel.se/upload/doc/support/usg/iPhone%20Whitepaper.pdf
As an aside, step# 8 on the page below advises to create a policy route using the source as the tunnel, which allowed me to browse the net on the client connected to the site VPN. Again, thanks for all the work.
https://kb.zyxel.com/KB/searchArticle!gwsViewDetail.action?articleOid=015533&lang=EN
Hi,
another vpn problem here. Trying to connect Android 12 through L2TP VPN.
I have USG20-VPN with latest firmware. I ran the wizard and everything should be fine. If I disable security policy all together VPN works and I can connect with my phone. But when it’s on the connection gets blocked by Default security rule.
Example:
Message; Source; Destination; Note
Match default rule, DROP [count=6]; android_public_ip:43858; wan_ip:1701; ACCESS BLOCK
and just before that comes this
Dynamic Tunnel [***:***] built successfully
Stuck there as well – any update?
Got it, I had a security policy twisted up. Works now!
Did everything according to this guide, but in my logging I only see my android phone trying to connect on the ZyWall, port 500. That is granted (just like in the log screenshot in this tutorial), but nothing happens afterwards. Nothing in the logs, too.
Any help?